Initialize Hybird HPC
Attention: This function only supports LiCO clusters whose operating system is RedHat 8.6
Install Hybrid HPC--Azure.
# config EPEL repo dnf install -y https://dl.fedoraproject.org/pub/epel/epel-release-latest-8.noarch.rpm # install dnf install -y lico-core-cloudscheduling-azureModify the configuration file
/etc/lico/lico.ini.d/cloudscheduling.ini, and change the following content to the IP address and subnet mask of the LiCO management node:[CLOUDSCHEDULING] # local head node ip address/netmask # for example: # inet 10.241.57.123/24 brd 10.241.57.255 # HEAD_NODE_ADDRESS = "10.241.57.123/24" HEAD_NODE_ADDRESS = "127.0.0.1/24"The LiCO management node shares
/opt/lico/cloud:echo "/opt/lico/cloud *(ro,sync,no_subtree_check,no_root_squash)" >> /etc/exports exportfs -aModify the LiCO management node slurm configuration file
/etc/slurm/slurm.conf, and add the following content at the end of the file:include /opt/lico/cloud/azure/slurm.confRun the following command to restart the slurmctld service on the LiCO management node:
systemctl restart slurmctldCreate an Azure Authenticator:
Register an application Attention: Before registering the application, please check your Azure AD permissions and subscription permissions. For details,please refer to https://learn.microsoft.com/en-us/azure/active-directory/develop/howto-create-service-principal-portal
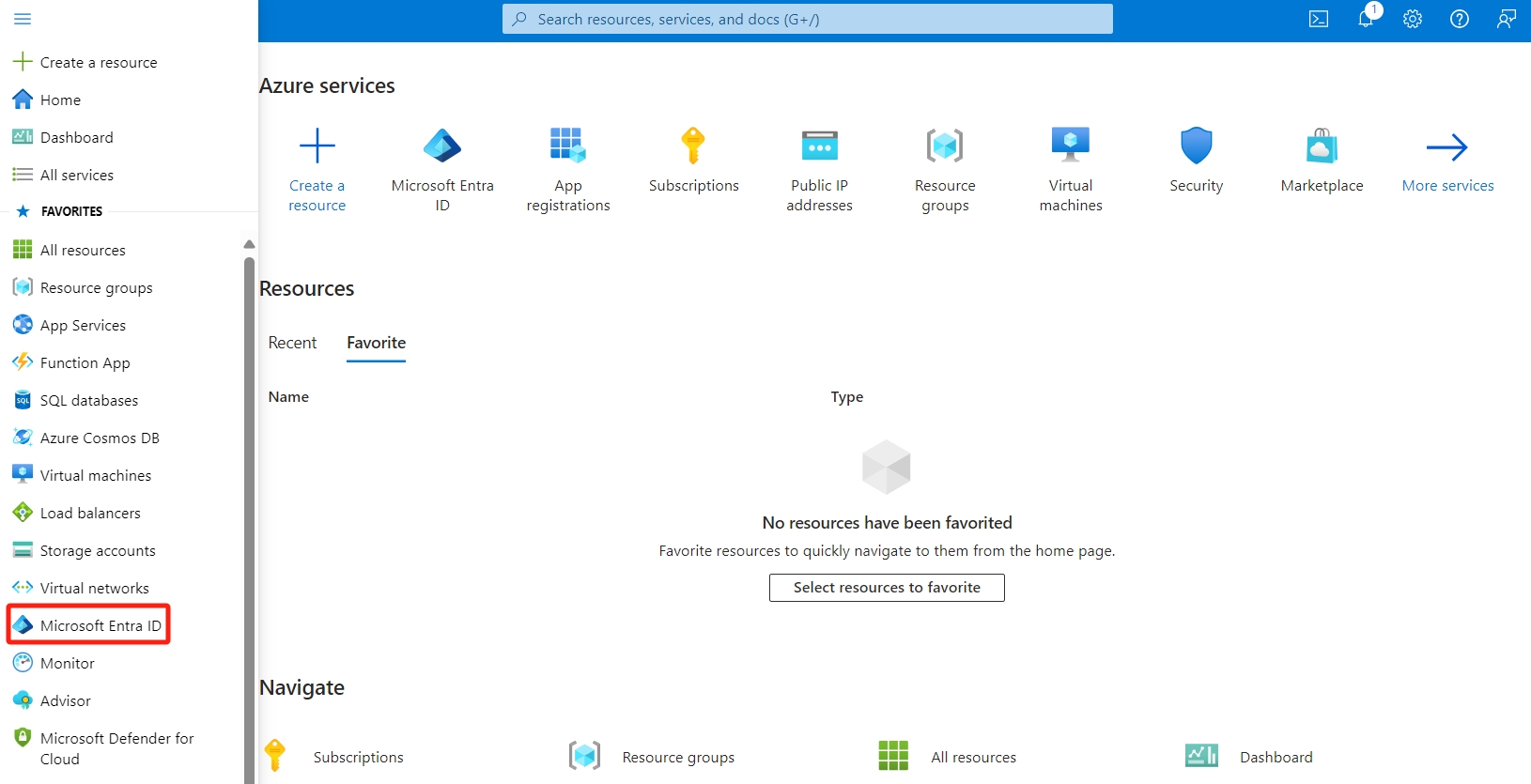
Sign in to your Azure Account through the Azure portal and select Azure Active Directory
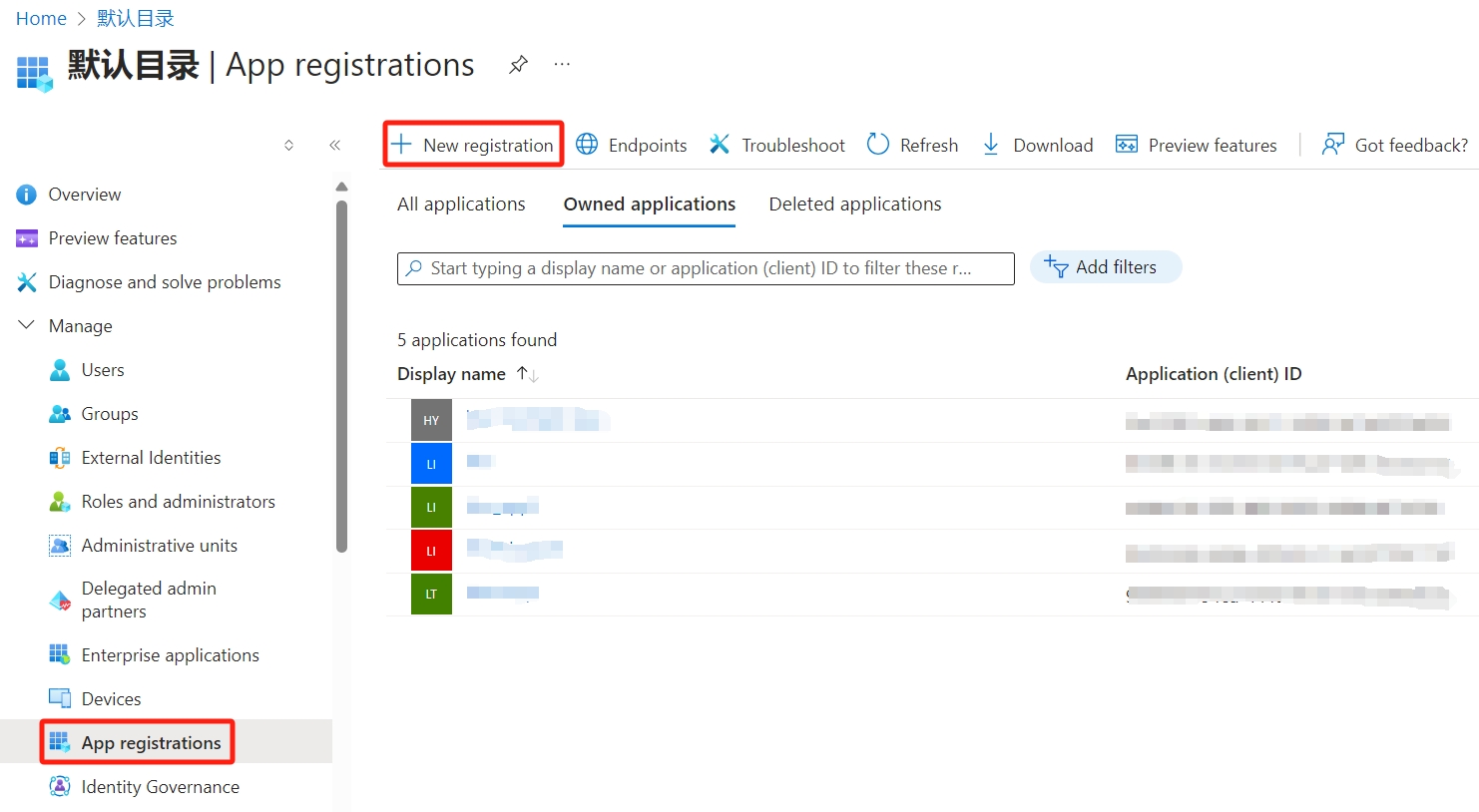
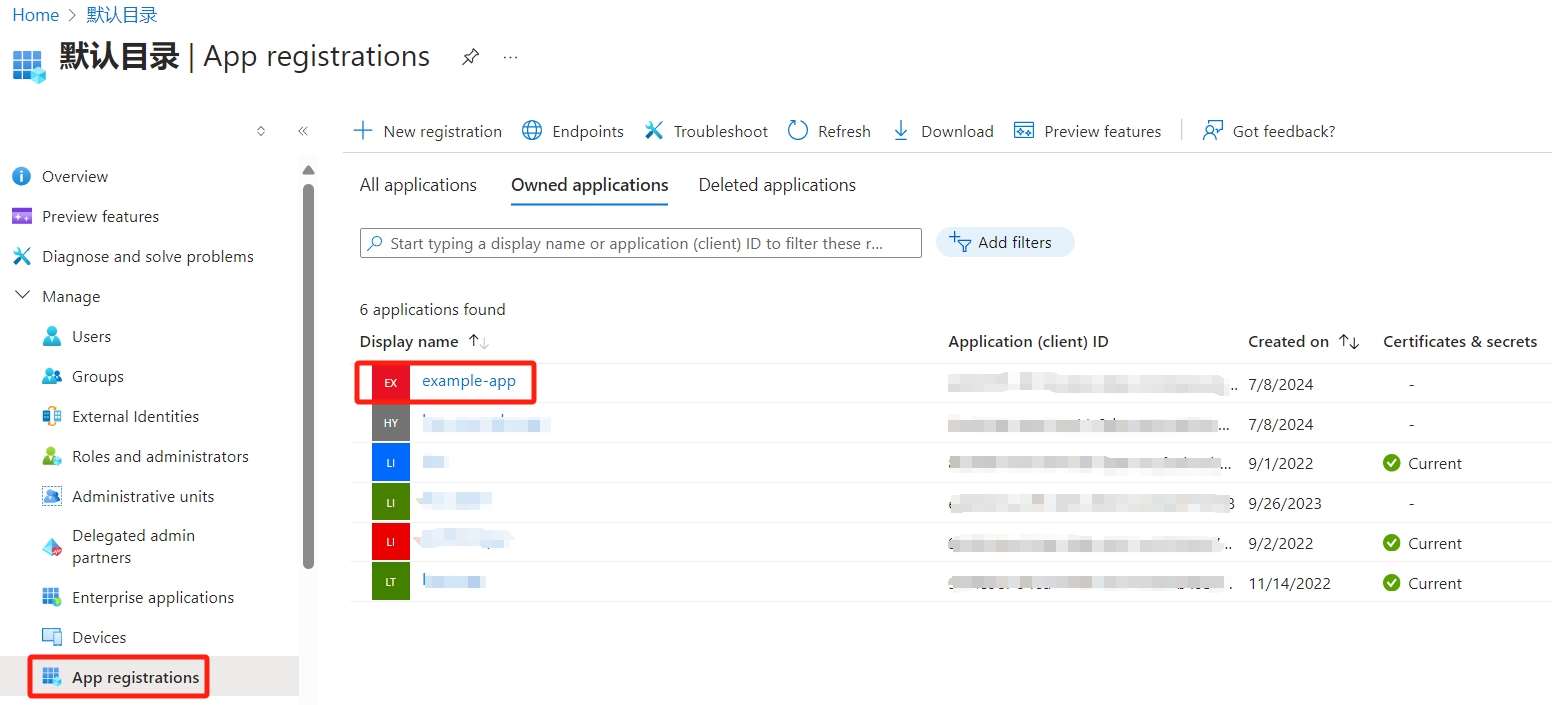
Select App registrations and Click New registration
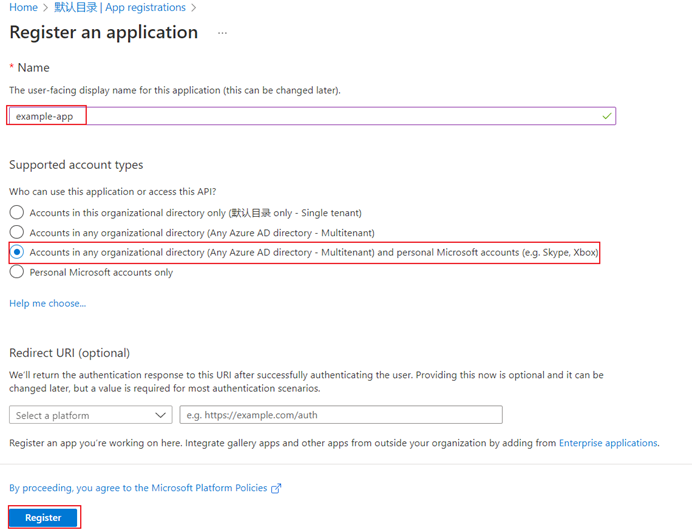
Name the application, for example example-app. Select a supported account type, which determines who can use the application. After setting the values, select Register.
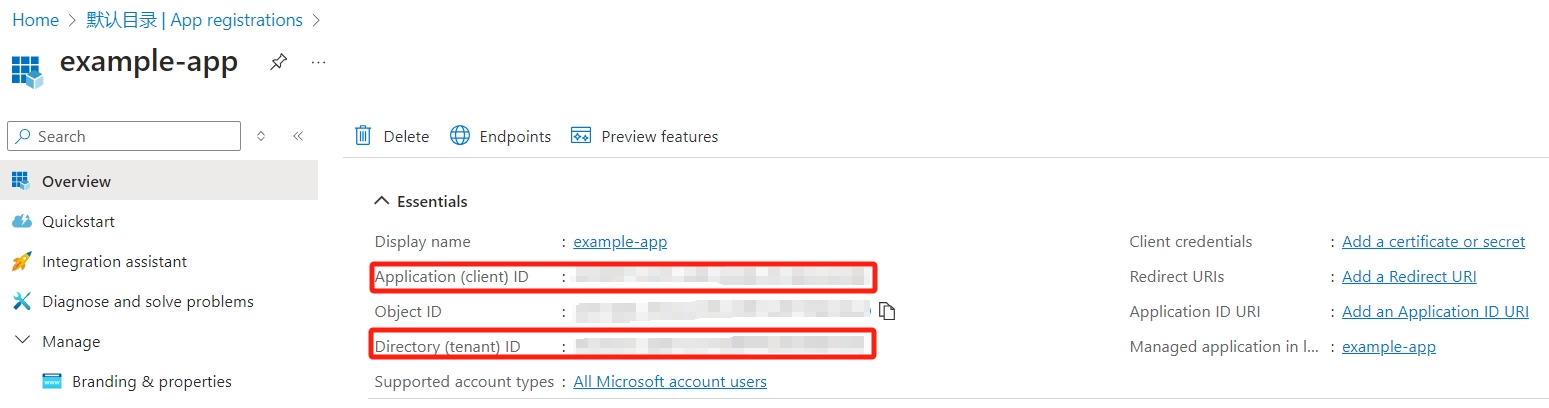
After registration is complete, copy the Application (client) ID and Directory (tenant) ID and store.
Assign a role to the application
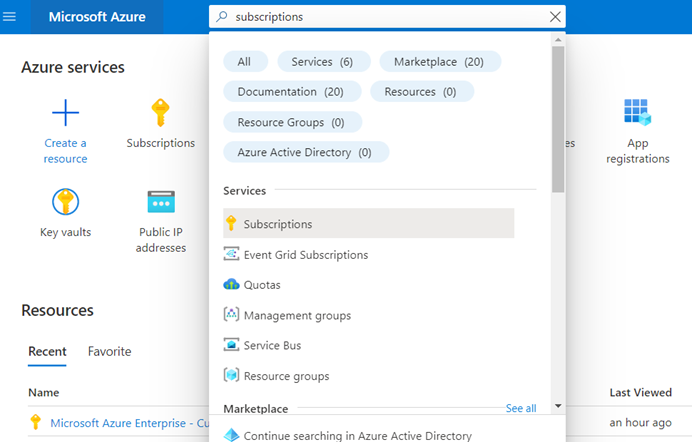
In the Azure portal, assign a role at the subscription scope, search for and select Subscriptions, or select Subscriptions on the Home page.
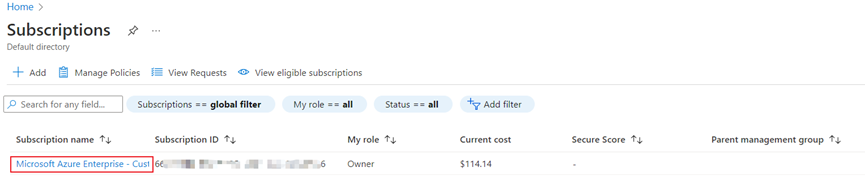
Select the particular subscription to assign the application to.
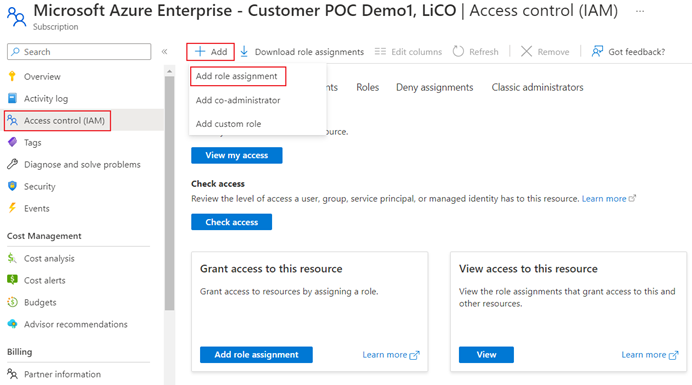
Select Access control (IAM), Select Add > Add role assignment to open the Add role assignment page.
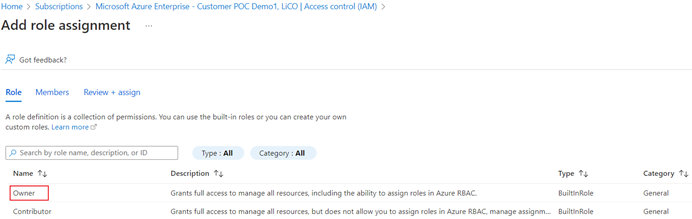
In the Role tab,select Owner
In the Members tab,Select Assign access to-> User, group, or service principal and then select Select members. By default, Azure AD applications aren't displayed in the available options. To find your application, search by name (for example, "example-app") and select it from the returned list. Click the Select button.
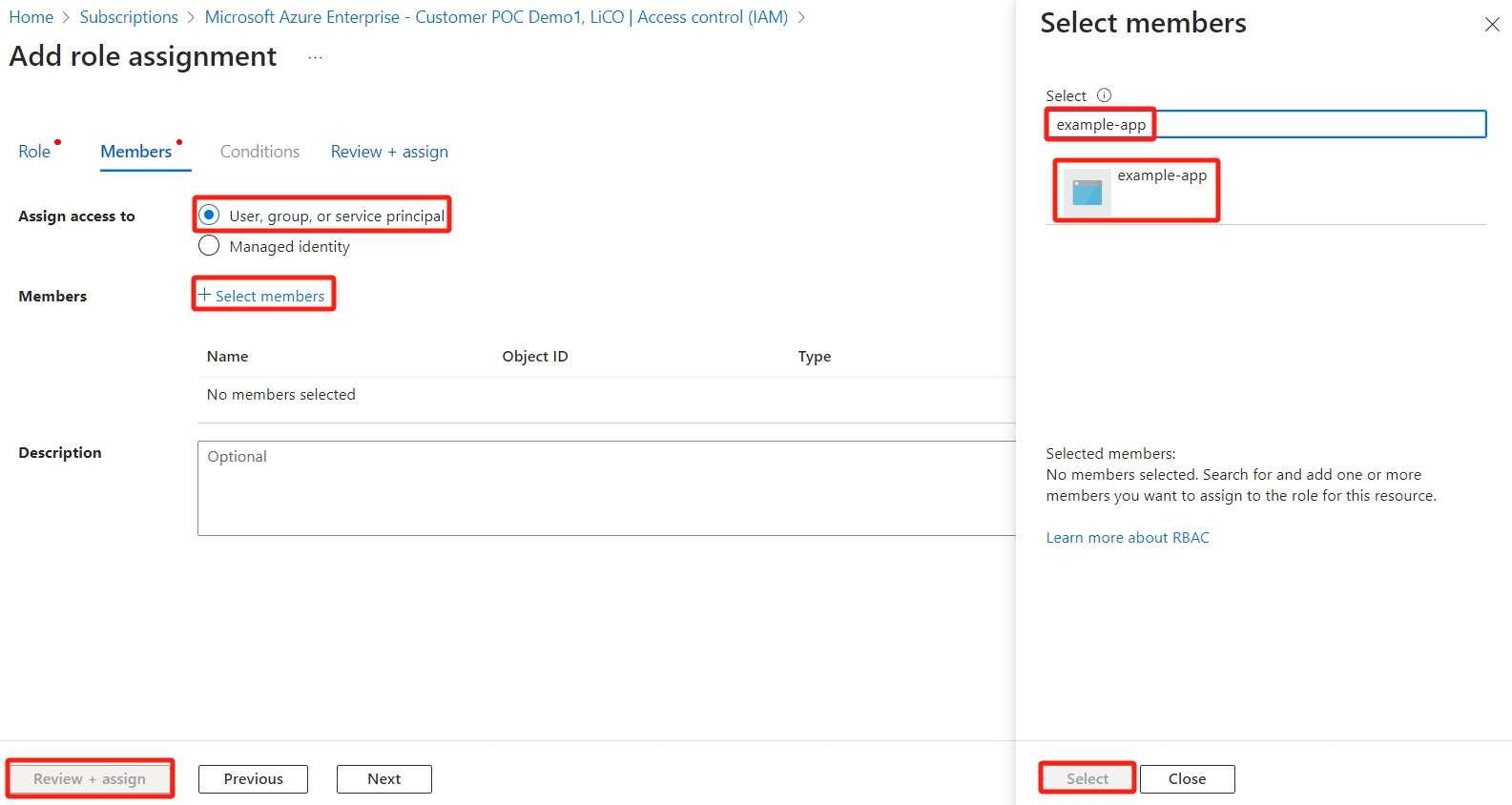
Then click the Review + assign button
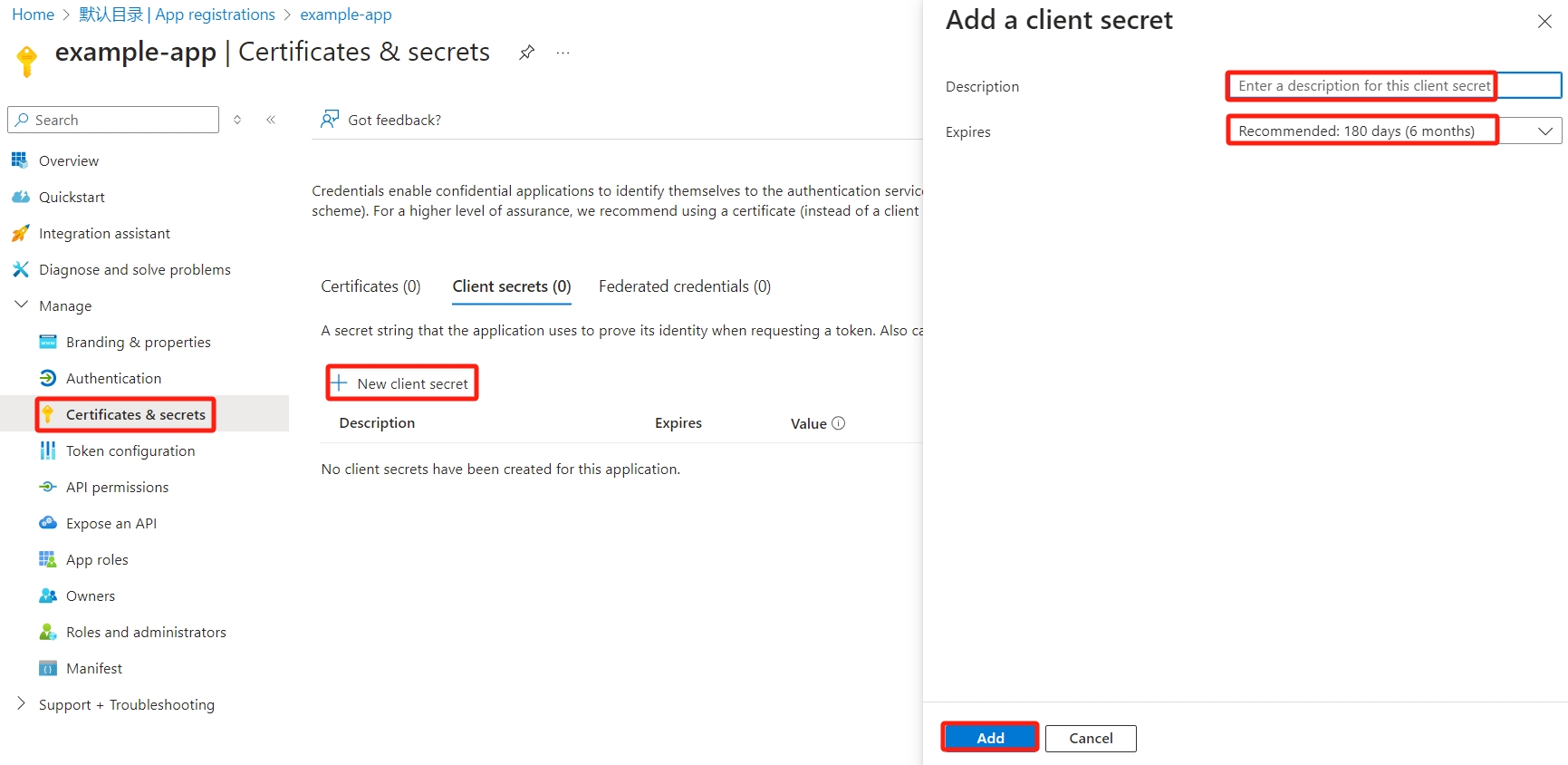
Create a new application secret
Select Azure Active Directory
From App registrations in Azure AD, select your application.
Select Certificates & secrets
Select Client secrets -> New client secret.
Provide a description of the secret, and a duration. When done, select Add.
After saving the client secret, the value of the client secret is displayed. Copy this value because you won't be able to retrieve the key later.Store this value in the same location with the tenant ID and application ID.
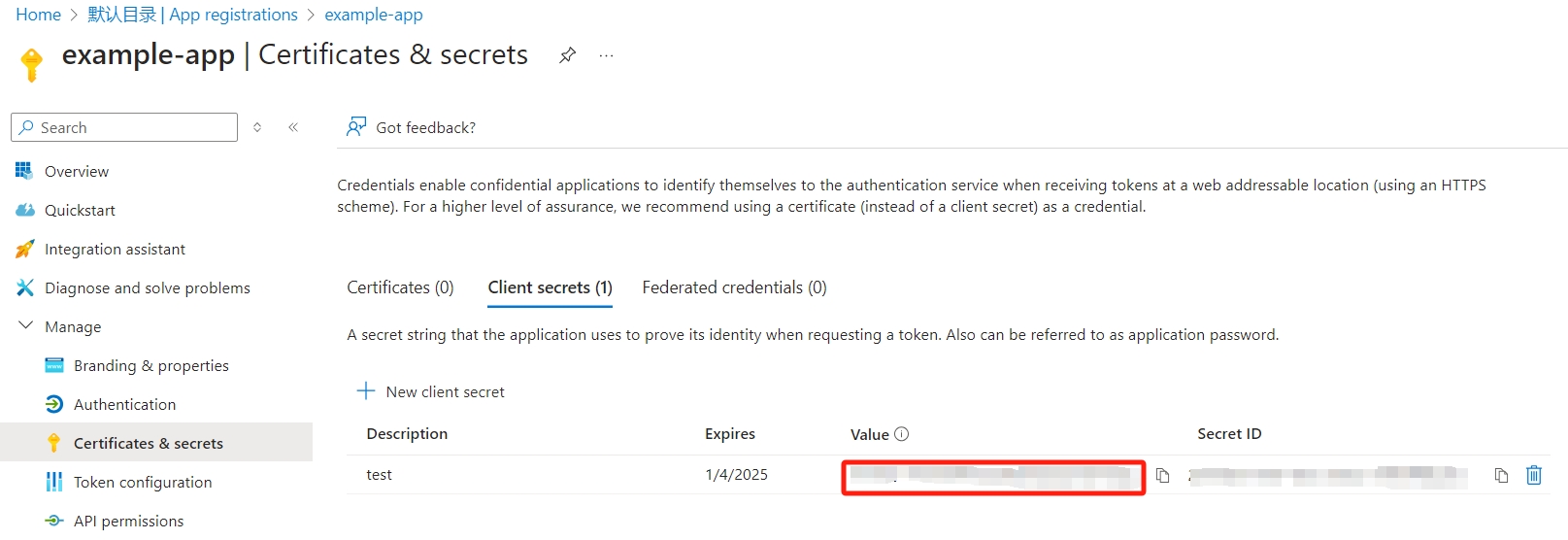
Run the following command to import the azure authentication information into LiCO:
# Import the application (client) ID, directory (tenant) ID and client password obtained in 6. # Follow the prompts and import them in sequence lico azure_secret import